CloudThinker integrates with 15+ alerting and monitoring platforms including PagerDuty, Datadog, Grafana, Prometheus, AWS CloudWatch, Azure Monitor, GCP Monitoring, and more. Each integration includes platform-specific field mapping, flexible authentication, and automatic AI investigation triggers.Documentation Index
Fetch the complete documentation index at: https://docs.cloudthinker.io/llms.txt
Use this file to discover all available pages before exploring further.
Supported Platforms
Incident Management
PagerDuty
Authentication: HMAC-SHA256On-call management and incident response with native event mapping for triggered, acknowledged, and resolved events.
Opsgenie
Authentication: API KeyAtlassian’s alert management with priority mapping and team assignment data.
ServiceNow
Authentication: API KeyEnterprise IT service management with CMDB CI mapping for infrastructure context.
BigPanda
Authentication: Bearer TokenAIOps event correlation and alert management with intelligent alert grouping.
Monitoring & Observability
Datadog
Authentication: Bearer TokenFull-stack monitoring with metrics, alerts, and tag-based service correlation.
Grafana
Authentication: Bearer TokenAlert notifications with dashboard links, panel context, and common labels extraction.
Prometheus / Alertmanager
Authentication: Bearer TokenNative Alertmanager webhook receiver with label extraction, grouping support, and Kubernetes metadata.
Splunk
Authentication: Bearer TokenSaved search alerts with result context and search links.
Cloud Provider Alerting
AWS CloudWatch
Authentication: API KeyEventBridge-based alerting with alarm state, metric data, and namespace context.
Azure Monitor
Authentication: NoneCommon Alert Schema support with resource context and severity mapping.
GCP Monitoring
Authentication: Bearer TokenIncident notifications with policy details and resource display names.
APM & Error Tracking
New Relic
Authentication: API KeyFull-stack observability with issue priorities and entity context.
Dynatrace
Authentication: API KeySoftware intelligence with problem impact analysis and AI-detected root causes.
Sentry
Authentication: HMAC-SHA256Application error tracking with issue details, stack traces, and project context.
Custom Integration
Generic Webhook
Authentication: Bearer Token (configurable)Fully customizable webhook for any platform. Define your own field mappings using JSONPath expressions.
Platform Roadmap: Don’t see your platform listed? Use the Generic Webhook for immediate integration, or contact support to request a native connector for your monitoring tool.
Setting Up a Webhook Integration
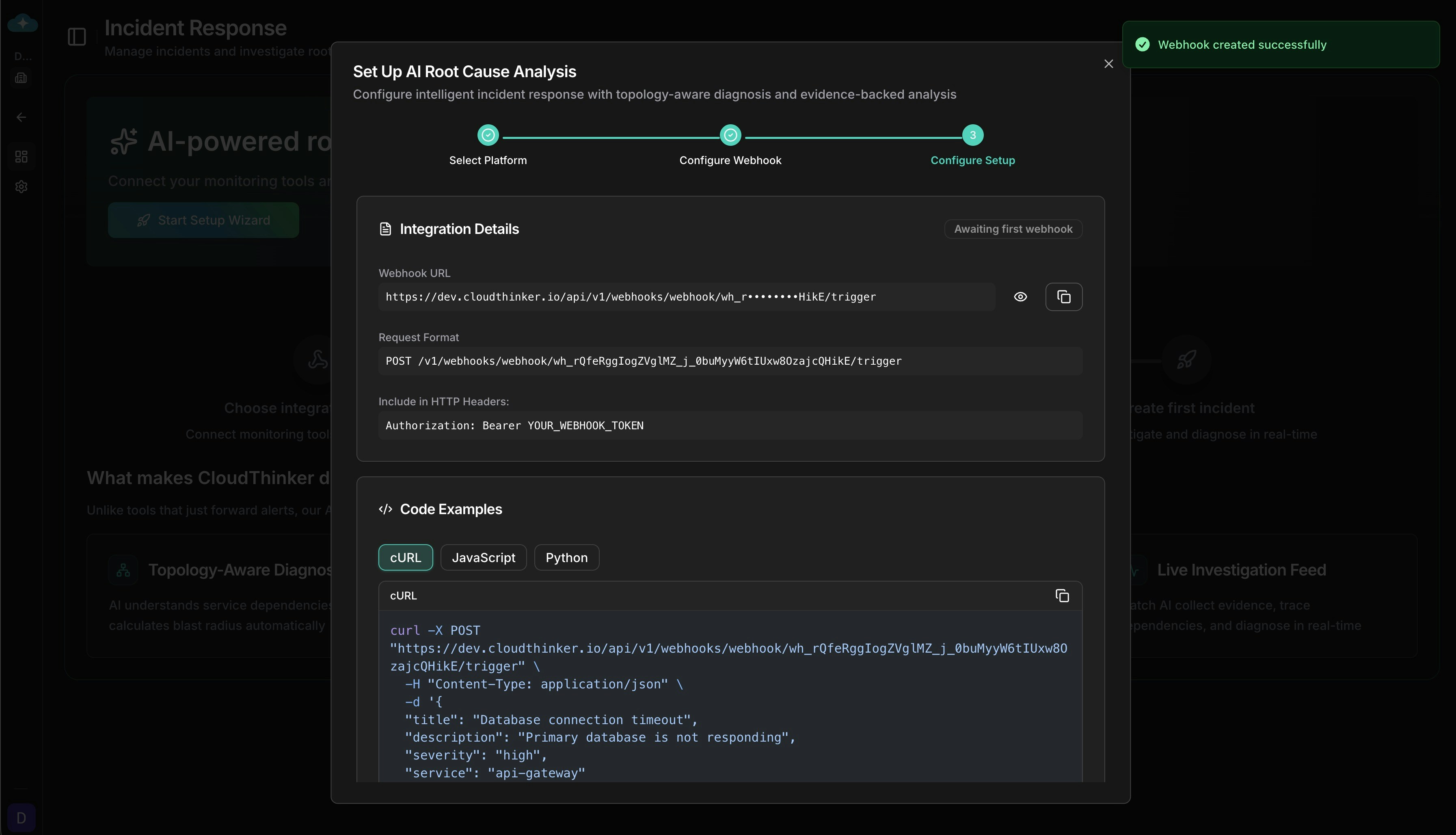
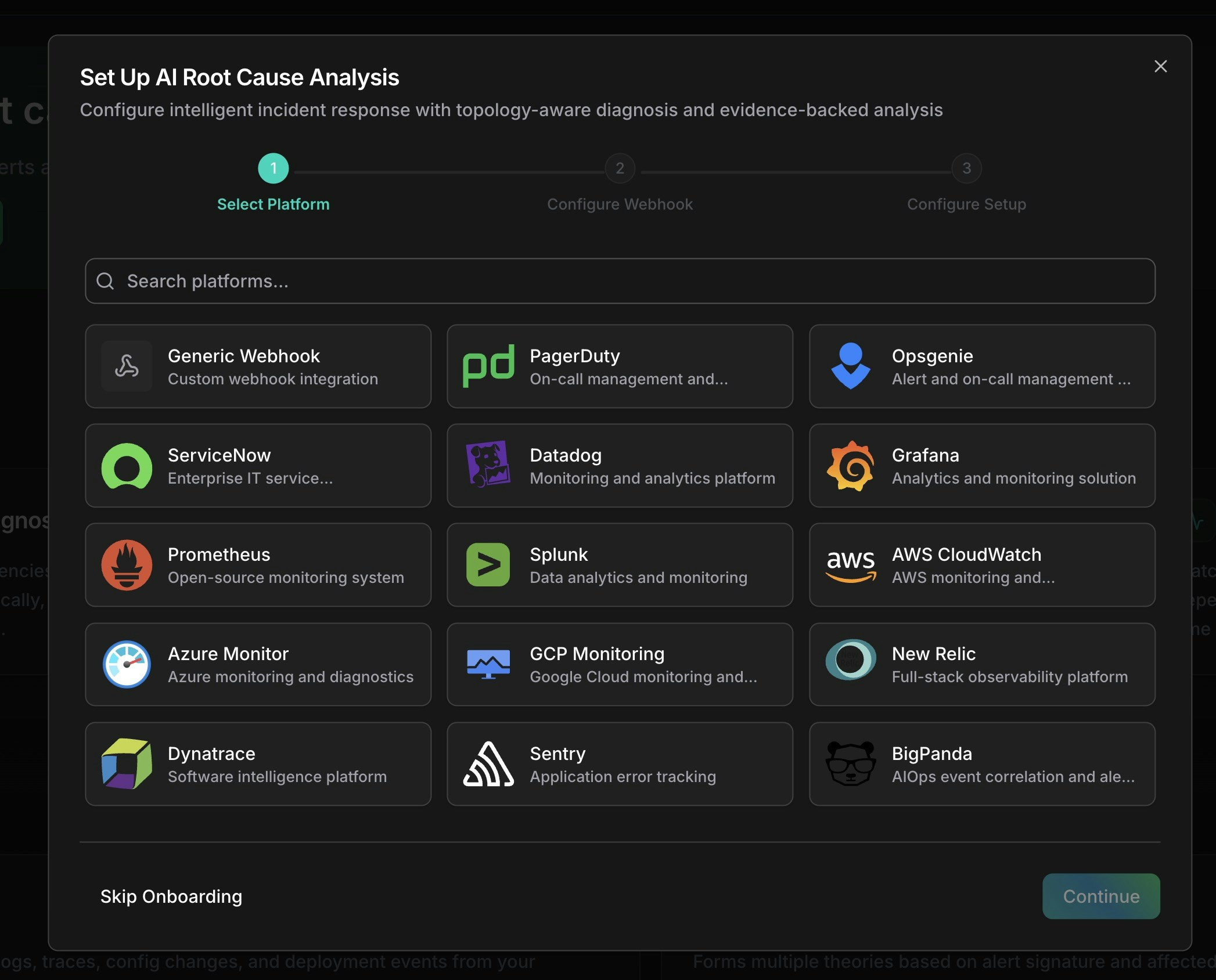
The setup wizard guides you through platform selection, webhook configuration, and automatic root cause analysis settings.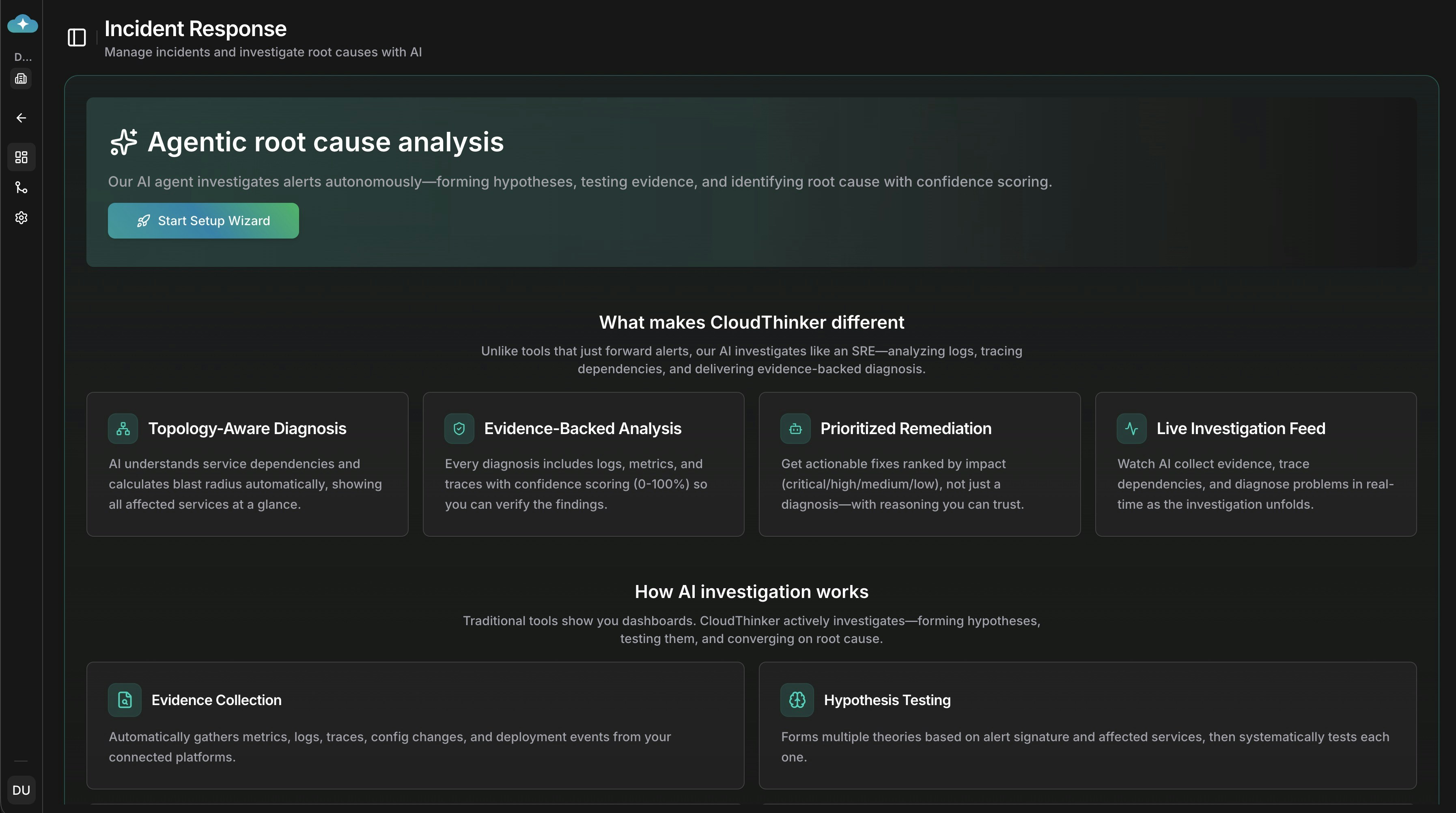
Incident Response dashboard with setup wizard entry point
Navigate to Integrations
Go to Incidents → Settings → Integrations tab to access webhook management.
Create Webhook
Click Connect on your platform card. The creation wizard opens with platform-specific defaults pre-configured.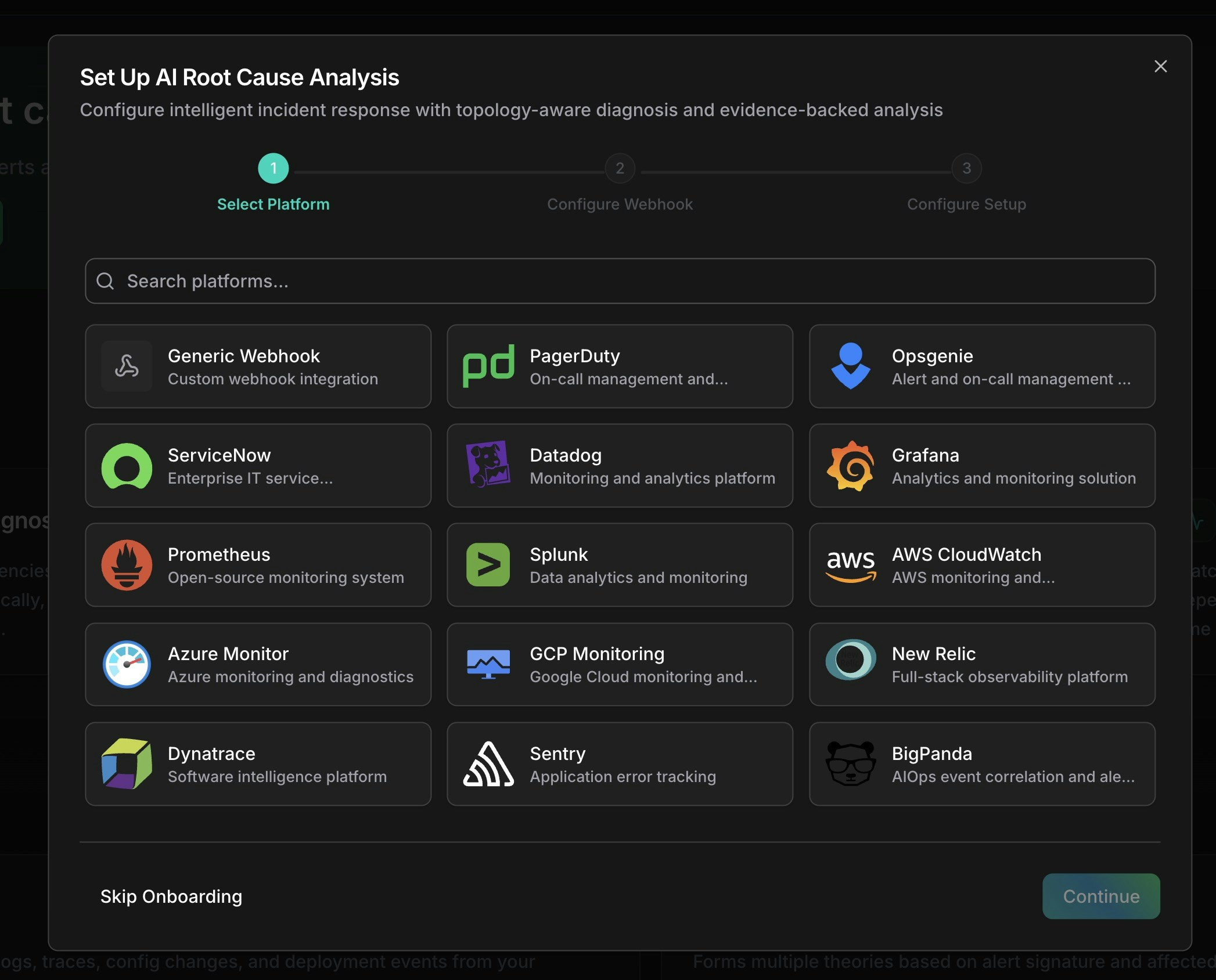
Select your monitoring platform from the available options
Configure Basic Info
Enter a name and optional description for your webhook. Set a rate limit if needed (default: 100 requests per hour).
Review Field Mapping
Each platform has pre-configured JSONPath mappings that extract incident fields from your webhook payload. Customize if needed:
You can also configure severity mapping to translate your platform’s severity values (e.g., 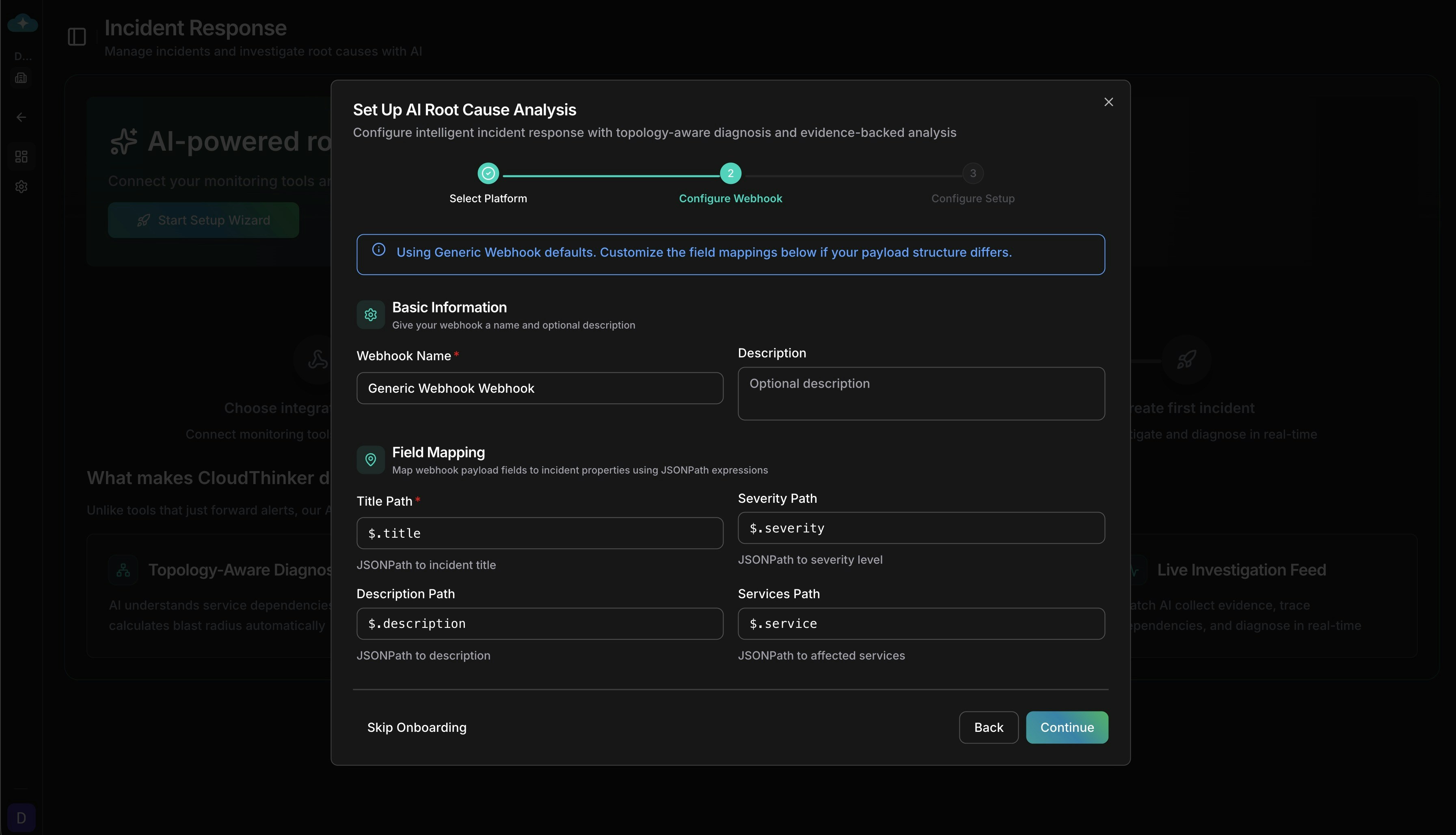
| Incident Field | Example JSONPath | Description |
|---|---|---|
| Title | $.event.data.title | Incident headline |
| Description | $.event.data.description | Detailed information |
| Severity | $.event.data.priority | Critical, High, Medium, Low, Info |
| Services | $.event.data.service.name | Affected service names |
warning → medium, P1 → critical) to CloudThinker’s severity levels.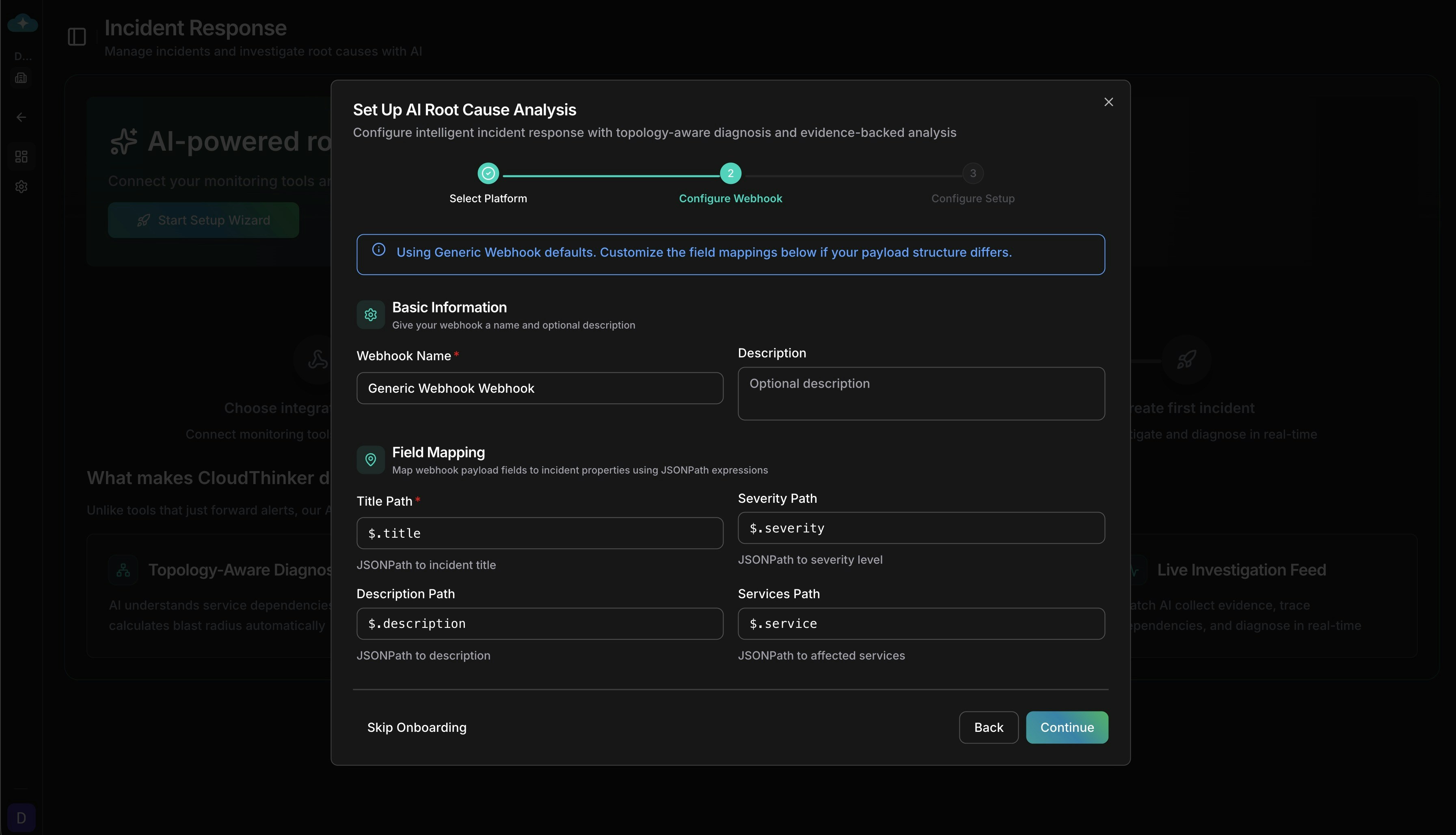
Configure JSONPath field mappings for your webhook payload
Configure Auto-Trigger Settings
Control how incidents trigger Root Cause Analysis: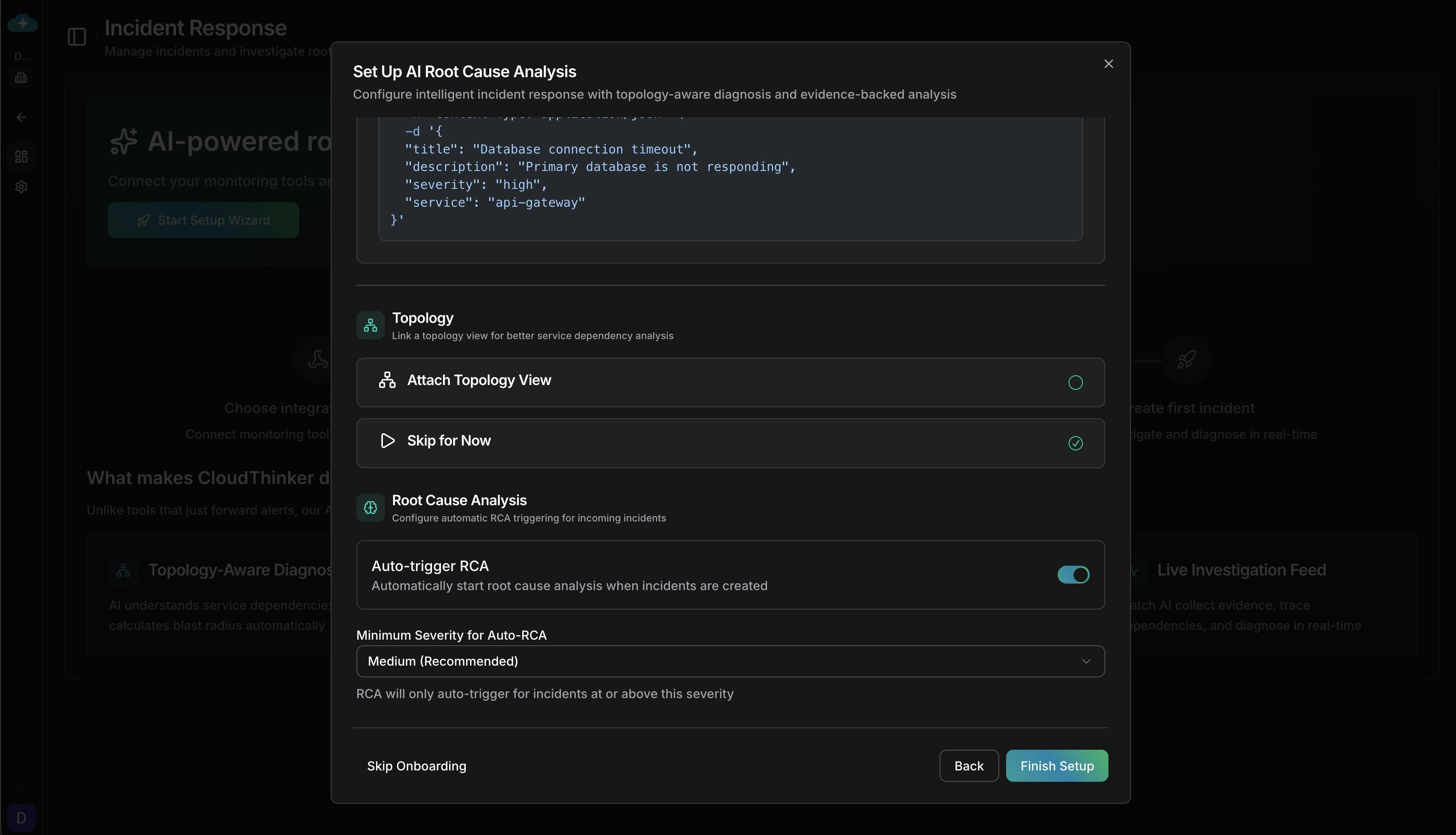
- Auto-trigger RCA: Automatically start AI investigation when an incident is created
- Minimum severity: Only trigger RCA for incidents at this severity level or higher (default: Medium)
- Send all fields to agent: Forward the complete webhook payload to the RCA agent for richer analysis
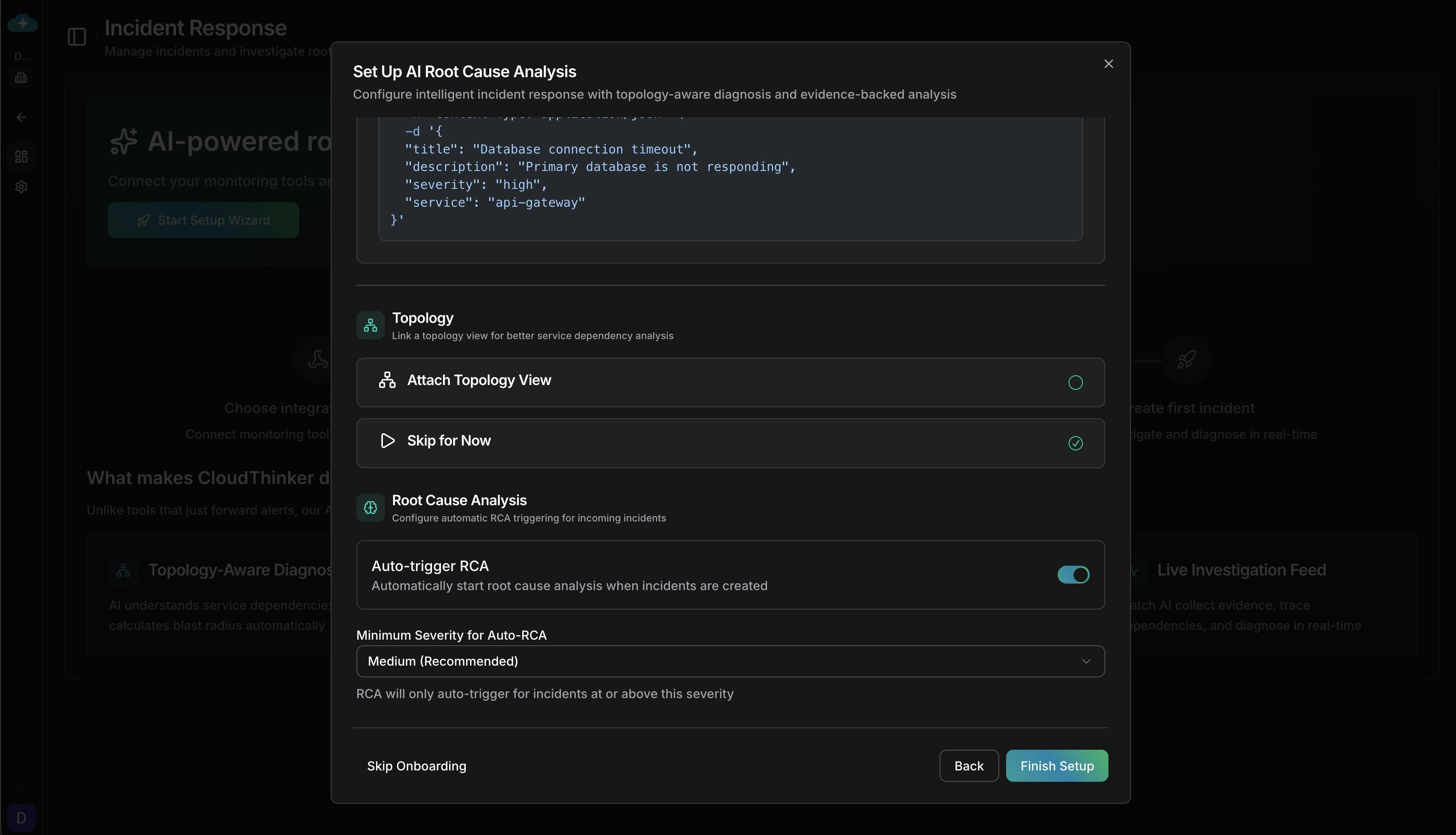
Configure automatic RCA triggering and severity thresholds
Authentication Methods
CloudThinker supports four authentication methods to match your platform’s requirements. The correct method is pre-selected when you choose a platform, but you can change it for custom integrations.| Method | How It Works | Used By |
|---|---|---|
| Bearer Token | Standard token-based authentication via Authorization header | Datadog, Grafana, Prometheus, Splunk, GCP Monitoring, BigPanda |
| HMAC-SHA256 | Cryptographic signature verification — CloudThinker validates the request body signature using a shared secret | PagerDuty, Sentry |
| API Key | Custom header with optional prefix (e.g., GenieKey, Api-Token) | Opsgenie, New Relic, Dynatrace, ServiceNow, AWS CloudWatch |
| No Authentication | For platforms that verify identity through other mechanisms | Azure Monitor |
When you change the authentication method on an existing webhook, existing integrations using the previous method will immediately stop working. Regenerate credentials after changing auth methods.
Alert Correlation
When multiple alerts arrive within a short time window, CloudThinker can automatically correlate them into a single incident instead of creating duplicates. This reduces alert fatigue from cascading failures.Time Window Correlation
Groups alerts received within a configurable window (default: 5 minutes). When a new alert matches an existing open incident, it’s attached as a correlated alert rather than creating a new incident.Rule-Based Correlation
Define custom rules to match incoming alerts against existing incidents based on shared attributes. Rules are configured from the webhook card menu under Correlation Rules. Each rule specifies:- Conditions with AND/OR logic for matching
- Priority (0-1000) to control evaluation order
- Weight (0.0-1.0) to indicate match confidence
- Minimum match weight threshold to accept a correlation
| Operator | Description |
|---|---|
equals / not_equals | Exact match or mismatch |
contains / not_contains | Substring match |
starts_with / ends_with | Prefix or suffix match |
regex | Regular expression match |
in / not_in | Value in or not in a list |
intersects | Array overlap (e.g., shared tags) |
exists | Field is present |
Security & Limits
Payload Limits
| Limit | Value |
|---|---|
| Max HTTP body size | 1 MB |
| Max stored payload size | 100 KB |
| Max field length | 10,000 characters |
| Max array items | 100 elements |
| Max nesting depth | 10 levels |
Rate Limiting
| Limit | Value |
|---|---|
| Default rate limit | 100 requests per hour per webhook |
| Auth failure limit | 10 failures per 15-minute window |
| Exceeded response | HTTP 429 |
Security Features
- Timing-safe signature verification prevents timing attacks on HMAC validation
- Encrypted secret storage — webhook secrets are encrypted at rest
- Credential rotation — regenerate webhook tokens and secrets without recreating the webhook
- Payload sanitization — oversized fields are automatically truncated
- Sensitive header filtering — authentication headers are excluded from audit logs